Network Attacks in Real Time Scenario Over Campus Network
| ✅ Paper Type: Free Essay | ✅ Subject: Computer Science |
| ✅ Wordcount: 2923 words | ✅ Published: 12 Mar 2018 |
Amit Mahajan* Vibhakar Mansotra**
ABSTRACT
This paper presents study of attacks in real time scenario over the campus network. The attacks were monitored over a time and analyses were made. The paper discusses about the dependency over the IDS/IPS signatures and proposes for a solution which records the events with raw traffic and visualizes the traffic to give better understanding of the behavior of the traffic flow over the network.
Keywords: UTM, Attacks, Visualization, Afterglow, tcpdump.
I INTRODUCTION
Networks have been under attack from the time Internet came into existence. There is consistently some lack of determination connected with the effect of these attacks. In the present situation of PC innovation, any institution can have enormous machine frameworks of distinctive natures. With the advancement of technology, Organizations have started facing difficulties due to different types of computer viruses and attacks. This resulted in tremendous loss of the internal assets like data and utility of time. Thus there is an urgent need to study these attacks and network breaches by means of which one will be able to devise preventive measures and thereby protect the internal assets.
In view of the above objectives one has to understand the networks and how they expand widely. Also one has to understand the attacks and breaches. Mostly the internet is one of the sources of the viruses and attacks but quite often the local network is also a major source of threats for campus networks. Generally administrators and organizations safe guard their networks from outside threats but the internal attacks and breaches are very crucial. The IDS/IPS ( ) are installed over the gateway level to scan the outgoing and incoming traffic. Where these kind of mechanism to study the behavior of internal attacks is vague. One is very much interested in knowing the kind of traffic flow, and its identification etc in the network. This kind of approach will help the user community to adopt preventive measures or in other words one has obtain a solution by studying the internal attacks and network breaches and thereby how to minimize and protect the internal assets . Analysis of the network can be used as a tool to scan the network traffic. The behavior of the network may be understood through penetration tools, simulations etc. Alternatively a tool like IPS having capability of network behavior analysis also can be of great help in understanding the problem.
SURVEY OF WORK
Asmaa Shaker Ashoor and Sharad Gore in their research differentiated the Intrusion Detection System and Intrusion Prevention System (IDS/IPS) technology which is used in the computer networks. They compare the stability, performance and accuracy wise result of IDS and IPS. They highlighted that the major difference between the IDS / IPS is among their deployments over the network. IDS technology works on out band system which means it is not lined with the network path but IPS technology works on in-line with the system, means it can pass through in between the devices in real time.
Jared Holsopple, Shanchieh Jay Yang, and Moises Sudit discusses about the Present run-through for fighting cyber-attacks which are typically used by the Intrusion Detection Sensors (IDS) to inactively detect and block multi-stage attacks. The algorithm, TANDI, helps in reducing the problem difficulty by separating the simulations of the attacker’s capability and opportunity and thus fuses the two to determine the attacker’s intent. The results of the research demonstrate that the algorithm TANDI predicts that the future attack action precisely as long as it is not a coordinated attack and which contains no internal threats. In the presence of the malicious attack events, the algorithm TANDI, will give alarm to the network analyst for further analysis. This can be further analysed with the help of simulation.
Nilima R. Patil and Nitin N. Patil in their paper discussed about the importance of attack graph to check the possible attacks in the network. Using attack graph, analysis can be done effectively. This helps the administrators to further analyze the attack graphs deeply to know where their system weaknesses lie. Accordingly help them to decide what kind of security measures can be opted for effective deployment. They study different ways to analyse attack graphs and to provide future scope for research on these attack graphs.
Rosslin John Robbles, Tai-hoon Kim, Seung Lee in their paper have shown that a second level in addition to access control intrusion confinement can dramatically enhance the security especially integrity and availability of a system in many situation. It showed that intrusion confinement can effectively resolve the conflicting design goals of an intrusion detection system by achieving both a high rate of detection and a low rate of errors. Developing a more concrete isolation protocols will further be studied in the future research.
Meera Gandhi and S.K Srivastava in their paper highlighted the importance of Intrusion detection in business sector and in active area of research. They describe IDS as important tool for information security. An IDS is intended to identify and fight with some common attacks over the network systems. In such systems log displays the list of attacks to the administrator for ambiguous action. This system works as an observant device in the event of attacks directed towards an entire network.
In the light of the above available information a need has been felt to undertake similar type of work in the University of Jammu as well. This will help in study of attacks received by the network of the campus. The network is setup on optical fiber backbone with around 100 distributed switches across the campus. Which also has WI- FI wireless Connectivity with access points around 200 approx. Such an ICT facility available over the network is plays an important role in helping the students, researches, teacher and staff. The number of users in the UOJ campus network appxo 3000. Thus the analysis of the attacks is taken up in this campus.
II EXPERIMENTAL SETUP USING UTM
University of Jammu is one of the pioneer higher educational institutes in the state of Jammu and Kashmir, India. Whose vision is to be an internationally competitive academic and research institution? To achieve University of Jammu has lot of focus on the information technology. In 2003 university started its initiatives to be an IT enabled university by setting up a university campus network on optical fiber backbone. Later this network was further converged with Jammu University JU Wi-Fi. This facility is playing a very crucial role in order to help the students, teachers, researchers and administrative staff to use the ICT facilities available over the network. University of Jammu is having huge internet bandwidth connectivity’s to cater the needs of the university fraternity. This internet bandwidth connectivity’s constantly keeps on upgrading from time to time. At present university is having 40 mbps Internet bandwidth 1:1 OPTICAL FIBER lease line from reliance and 1 Giga optical fiber connectivity from National Knowledge Network. Students, researchers and teaching faculty are able to access the scholarly contents online from any location within the campus. There are around 37 departments comprising of teaching and centers other than administrative blocks which are connected through this optical fiber back bone network. All the three girls and boys hostels are also connected through the optical fiber backbone. There are around 100 distributed switches (Cisco and Dlink) and approx. 200 indoor wireless access points (Linksys and Dlink) and 18 outdoor access points (Dlink) which are installed at the various locations of these departments / blocks of the university. All the equipment’s are connected through optical fiber backbone to the control room campus network of the university with Cisco catalyst switches 4507R, 4506.
In order to maintain such vast network and ICT Facilities University has deployed a UTM device in the network. This UTM device helps the university it administrators to maintain the university campus network more efficiently. UTM installed at the university is a product from world’s top IT security company Cyberoam. This UTM is installed almost all the major academic institutes of the country. The UTM device has multiple solutions in a single box. It comprises of load balancing of internet bandwidths, Antivirus and anti-spam scanning at the gate way level, User identity based firewall rules, gateway level IDS and IPS scanning and AAA authentications etc.
This UTM device is installed between the ISPS Routers and Cisco catalyst switches so that the whole traffic gets scanned through the UTM device. All the policies are applied on the firewall rules as per the requirement of the University network.
Figure: 1 UTM Deployment in Gateway Mode

With the increase in the University network and ICT facilities over this network, it is observed that the ratio of attacks also gets increased. These attacks reduce the performance of the University Network and other ICT facilities available. Thus to study the kind of attacks, their significance and a solution how to reduce them is proposed in this paper. UTM device installed in the University network is considered for collecting the IPS attacks data. Since it has the ability to produce the Attack reports, this will help the University IT administrators to see the trend of the attacks how they are generating and affecting the system. The critical IPS attacks will be studied over a time to find the patterns of the attacks and their significance over the network applications and ports to which they are associated. This study will help the university and other institutes which are using the same UTM to fine-tune the rules and other parameters so that network bandwidth and other services performance does not get affected with the attacks and users of the ICT facilities should have performance oriented service.
III DATA COLLECTION AND ANALYSIS USING UTM
As described in the previous about the network system university campus. The information on the number of IPS attacks has been collected since 1 July -2013 to 2-dec -2013 (22 weeks). The total number of attacks is 1301567. Out of these the type of attacks having frequency more than approx 100 is 1299646 lakh. These 13 lakh IPS attacks have been classified into 5 categories broadly example HTTP/ HTTPS, ICMP, UDP, FTP, TCP based on the signatures. The display of the number of IPS attacks belonging to each category is shown in figure-2:
Figure -2 Classifications of Attacks

Out of the above 13 lakh of the attacks the top 14 critical attacks from the five major categories have been identified to 162810 by the IPS and them display is shown in figure-3:

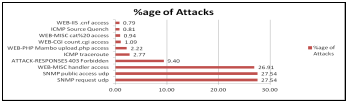
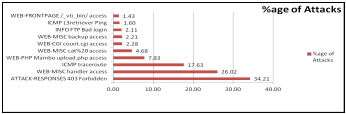
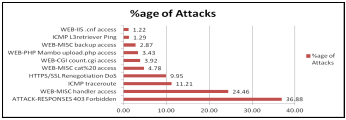
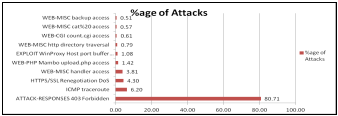
From the figure-3 it may be noted that the prominent attack having a frequency greater than equal to 4.38% are 6 types (responses 403 forbidden type is 45.62% , 17.38 % web misc handler access 8.57 % is https/ssl renegotion , 7.38% web php , 7.34% web cgi count , 4.38% info ftp bad login) . While rest of the 16 attacks less than 10 % are having very small frequencies. The percentage of attacks each of the 22 weeks is shown in the bar diagrams in figure series:
Week 1

Week 2

Week 3

Week 4

Week 5

Week 6

Week7
Week 8
Week 9
Week 10

Week 11
Week 12

Week13 
Week 14

Week15 
Week 16

Week 17

Week 18
Week 19
Week 20 
Week 21
Week 22
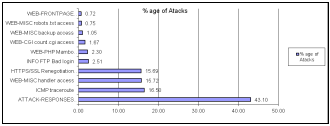
Out of 22 weeks, the percentage of Attack Responses 403 Forbidden is the most dominant one.
Forbidden attack response is the highest attacks with 45.62% overall in the 22 weeks, this incidence is generated when a 403 error response code is returned to a client by a web server, which indicates that an effort is made to take an unauthorized access to a web server or an application running on a web server. The 400 series error messages indicate an error on the part of the browser client making the request to a web server. The 403 response shows a request for a forbidden resource which cannot be gain access to even with authentication identifications. Many events can show a determined effort to exploit vulnerability on the victim’s server. Certain applications do not perform strict checks when confirming the credentials of a client host linking to the services offered on a host server. It can lead to an unauthorized access and probably escalated rights to that of the administrator. Information stored on the machine will be compromised and trust relationships established between the victim server and the other hosts that can be exploited by an attacker. In such Attack Scenarios; attacker can access the authentication mechanism and provide his/her own credentials to gain access. On the other hand the attacker can exploit the weaknesses to gain the administrator access without any exploit code.While the other prominent attacks are:-
ICMP trace route: This attack is generated when a Windows trace route (tracert) is detected. A trace route is be used to discover live hosts and network topologies. A Windows trace route command uses an ICMP echo request with a lower than normal Time to Live (TTL) value to identify live hosts and network topologies.
Web- MISC handler Attacks: this attack is generated when an attempt is made to exploit a known vulnerability on a web server or a web application resident on a web server.
The other attack which has very high severity level is the SNMP attack. From the figure- 4 shown below , it is noted that there is a peak in the number of attacks in the 8th (19-0ct-2013 and 9th week).It may be noted that this peak is due to SNMP attack responded by UDP with application whose activity is pronounced.
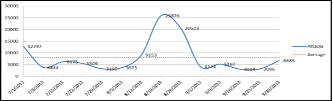
Figure: 4 shows16 different types of attacks out of 22 attacks per week are shown
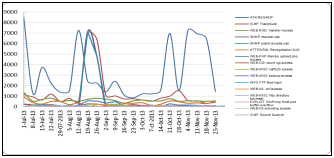
Figure –5 different types of major attacks per week
Figure: 5 Shows 16 different types of attacks out of 22 attacks per week are shown over the entire period. Of these 6 are found to be more conspicuous: – ATTACK-RESPONSES 403 Forbidden (ATK-RES403F) 71067, ICMP trace route (29205), WEB-MISC handler access (13959), SNMP request UDP (11954), SNMP public access UDP (11952), HTTPS/SSL Renegotiation DoS (7062)
IV FRAME WORK FOR EVALUATION AT THE GATEWEY LEVEL TO STUDY THE ATTACKS USING RAW PACKETS GENERATED BY THE NETWORK
To study the attacks more affectively, a frame work was deployed using open source software like Ubuntu, tcpdump with visualizing software like afterglow to capture real time at the core switch. This will help to monitor and analyze the network traffic in real time scenario. Data was evaluated for two hundred thousand packets captured using tcpdump –nnelr data.pcap l wc –l at the root.
This will capture the raw traffic for two hundred thousand packets for data analysis and visualization. The data captured by the tcpdump will be converted to a csv file with all fields.
Tcpdump-vttttnnelr ju.pcap|./tcpdump2csv.pl”timestamp sourcemac destmac sip dip sport dport flags len proto ttl id offset tos ipflags” > ju.csv.
The Csv file is then exported to Mysql database.
load data infile ’ju.csv’ into table analysis fields terminated by ’,’ lines terminated by ’n’ (timestamp, sourcemac, destmac, sourceip, destip, sourceport, destport, proto, tcpflags, length, ttl, ipid, iptos, ipflags, offset);
Further, ju.csv file was converted to dot file, which was converted to png file.
tcpdump -vttttnnelr Ju.pcap |./tcpdump2csv.pl|./afterglow.pl-c color.properties > Ju.dot
Cat Ju.dot | neato -Tpng –o Ju.png
Figure 6 shows Whole Traffic captured for network

Figure-6 shows that the outgoing traffic is greater than incoming traffic, which states that traffic is compromised. Therefore there is need to identify the port 80 traffic and identify the machines which are compromised. From figure 7 we identify visually that the out traffic on port 80 is very high. Therefore, needs to identify machines which are compromised.

Figure 7 shows the out going traffic of port 80

Figure -8 shows ATTACK from IP 192.176.2.25
Figure-8 Shows visualization of machine with IP 192.176.2 25 that is connected over the network which is compromised and sending malicious traffic outside. This helps the administrators to identify the machine irrespective of any signatures within the IPS database. Similarly other machines can be identified.
V CONCLUSION AND FUTURE SCOPE
IDS/ IPS are installed in almost every organization but they are designed to work on signatures. To study attacks which exist other than signatures, we need to further do the analysis through the frame work created with high end hardware which is required to capture and analyze the traffic for longer duration. So that fine tuning of the IDS/IPS as per the campus network requirement will be done to further increase the network performance.
VI REFERENCES
[1] Paxson. Bro: A System for Detecting Network Intruders
in Real- Time. In Computer Networks, volume 31 (23–
24), pages 2435–2463, 1999
[2] G. Stein, B. Chen, A.S. Wu, and K.A. Hua, “Decision
Tree Classifier for Network Intrusion Detection with
GA- Based Feature Selection,” Proc. 43rd ACM
Southeast Regional Conf.—Volume 2, Mar. 2005.
[3] Schwartz, Matthew, “Beyond Firewalls and IPS:
Monitoring Network Behavior.” February 2006,
available on http://esj.com/articles/2006/02/07/beyond-
Firewalls-and-ips-monitoring-networkbehavior.aspx
[4] S. J. Yang, J. Holsopple, and M. Sudit, “Evaluating Threat
Assessment for Multi-stage Cyber Attacks,” in Proceedings
of IEEE MILCOM: 2nd IEEE Workshop on Situation
Management (SIMA), Washington, DC, Oct 23-25, 2006
[5] Z. Yu and J. Tsai, “An efficient intrusion detection system
using a boosting-based learning algorithm”. International
Journal of Computer Applications in Technology, Vol. 27
(4), 2007, 223-231.
[6] Meera Gandhi, S.K.Srivatsa “Detecting and preventing
Attacks using network intrusion detection systems”
International Journal of Computer Science and Security,
Volume (2) : Issue (1) June 2009
[7] Asmaa Shaker Ashoor, Prof. Sharad Gore, “Intrusion
Detection System (IDS) &Intrusion Prevention System
(IPS): Case Study”. International Journal of Scientific &
Engineering Research Volume 2, Issue 7, July-2011
[8] Rosslin John Robles, Tai-hoon Kim,SeungLee,” A Study
on Intrusion Confinement for Internal Network”, Journal of
Security Engineering), vol.5issue no1, P73, 2008
[9] Patil, Nilima R.; Patil, Nitin N, ” A comparative study of
network vulnerability analysis using attack graph” World
Journal of Science & Technology; 2012, Vol. 2 Issue 3, p91
*University of Jammu, e-mail id :amit_ja2@rediffmail.com , **University of Jammu, email id: vibhakar20@yaho.com
1
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal



